Featured Brass Knuckles
-
2023 Classic Skull Head EDC Knuckles For Men
Regular price From $USD 84.99Regular priceUnit price per$USD 124.99Sale price From $USD 84.99Sale -
Afrankart DFK 2 Finger Brass Knuckles Ring Stainless Steel - Cakra EDC Gadgets
Regular price $USD 46.99Regular priceUnit price per$USD 66.99Sale price $USD 46.99Sale -
Brass EDC Self Defense Knuckles
Regular price $USD 94.99Regular priceUnit price per$USD 144.99Sale price $USD 94.99Sale -
2023 New Steel Knuckles
Regular price $USD 22.99Regular priceUnit price per$USD 38.99Sale price $USD 22.99Sale -
Afrankart DFK 2 Finger Brass Knuckles Knuckle Duster -Cakra EDC Gadgets
Regular price $USD 44.99Regular priceUnit price per$USD 62.99Sale price $USD 44.99Sale -
Folding Brass Knuckles 440C Stainless Steel
Regular price $USD 20.99Regular priceUnit price per$USD 32.99Sale price $USD 20.99Sale -
420 Stainless Steel Brass Knuckles Self Defense Real
Regular price $USD 20.99Regular priceUnit price per$USD 22.99Sale price $USD 20.99Sale -
2024 New Titanium Brass Knuckle
Regular price $USD 56.99Regular priceUnit price per$USD 86.99Sale price $USD 56.99Sale
Featured Self Defense Jewelry
-
2024 New Cross Self Defense Necklace
Regular price $USD 34.99Regular priceUnit price per$USD 46.99Sale price $USD 34.99Sale -
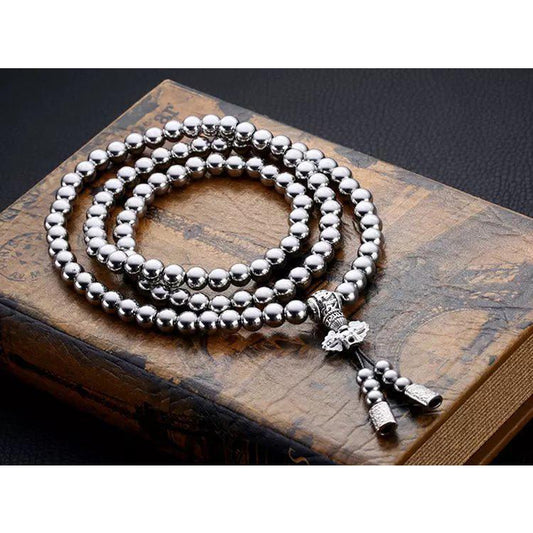
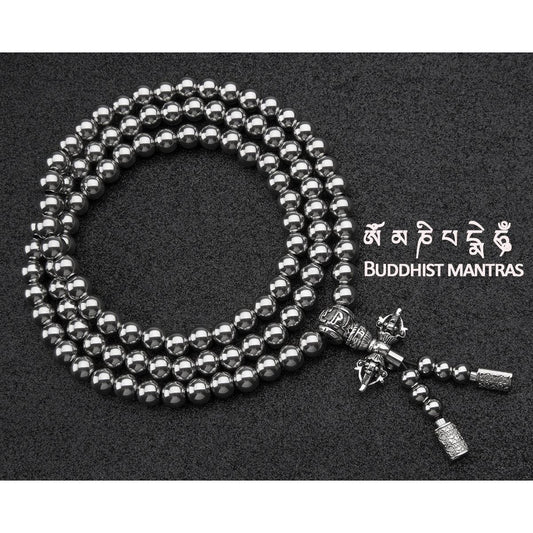
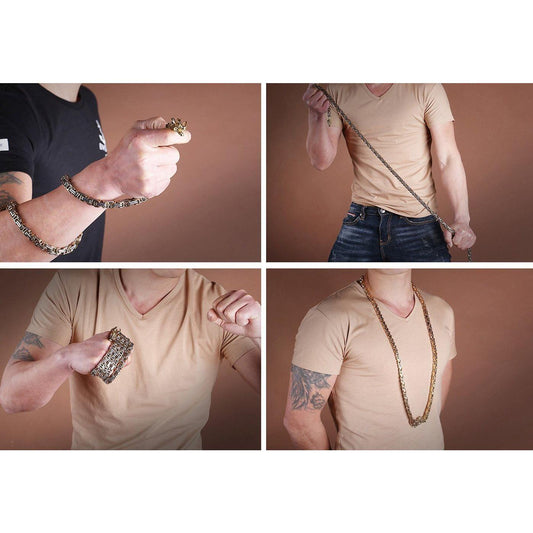
Full Stainless Steel Buddism Mala Self Defense Necklace EDC Defense Tool
Regular price $USD 28.99Regular priceUnit price per$USD 39.99Sale price $USD 28.99Sale -
Mahakala Self Defense Beads Mala Bracelet
Regular price $USD 28.99Regular priceUnit price per$USD 39.99Sale price $USD 28.99Sale -
Dragon Head Full Stainless Steel Self Defense Bracelet Jewelry
Regular price $USD 26.99Regular priceUnit price per$USD 36.99Sale price $USD 26.99Sale
Featured Self Defense Baton
-
Self Defense Tactical Whip With Stainless Steel Hammer Head
Regular price $USD 84.99Regular priceUnit price per$USD 108.99Sale price $USD 84.99Sale -
Self Defense Tactical Whip Stinger Legal Aluminium Alloy
Regular price $USD 28.99Regular priceUnit price per$USD 38.99Sale price $USD 28.99Sale -
Wooden Handle Stinger Self Defense Whip Car Emergency Tool For Women
Regular price $USD 20.99Regular priceUnit price per$USD 28.99Sale price $USD 20.99Sale -
Tactical Self Defense Whip
Regular price $USD 18.99Regular priceUnit price per$USD 28.99Sale price $USD 18.99Sale
Featured Self Defense Kubotan
-
Full 304 Stainless Steel Keychain Defense Baby Tonfa Kubotan
Regular price $USD 28.99Regular priceUnit price per$USD 36.99Sale price $USD 28.99Sale -
Tomahawk TC4 Titanium Kubotan Self Defense Stick
Regular price $USD 26.99Regular priceUnit price per$USD 38.99Sale price $USD 26.99Sale -
Push Dagger EDC Tactical Pen
Regular price $USD 18.99Regular priceUnit price per$USD 25.99Sale price $USD 18.99Sale -
Stainless Steel Self Defense Bamboo Kubotan
Regular price $USD 16.99Regular priceUnit price per$USD 22.99Sale price $USD 16.99Sale
Featured EDC Gadgets
-
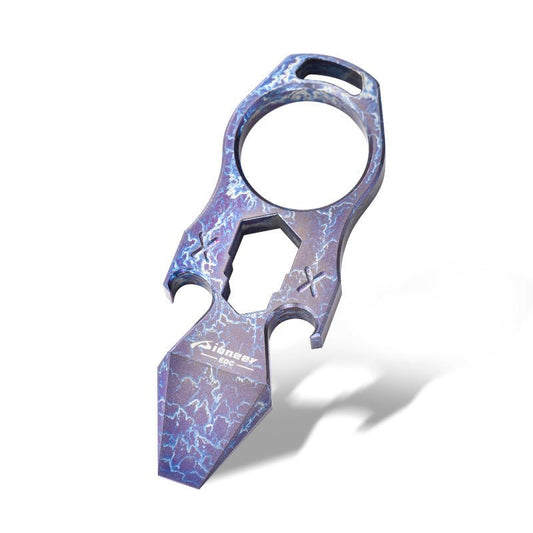
2023 NEW Titanium EDC Self Defense Keychain Multi Tool
Regular price From $USD 34.99Regular priceUnit price per$USD 48.99Sale price From $USD 34.99Sale -
TC21 Titanium Super Hard Tactical Cyclone Dagger Knife - Cakra EDC Gadgets
Regular price $USD 44.99Regular priceUnit price per$USD 64.99Sale price $USD 44.99Sale -
Spiked Brass Knuckles Ring Slingshot 404C Stainless Steel 3 In 1
Regular price $USD 46.99Regular priceUnit price per$USD 66.99Sale price $USD 46.99Sale -

 Sale
SaleTauren Push Dagger
Regular price $USD 24.99Regular priceUnit price per$USD 36.99Sale price $USD 24.99Sale